LEAP: The Redmond trip
 As I wrote in previous articles, the LEAP program consists of five masterclasses in The Netherlands and a set of presentations from Microsoft architects in the USA. Sunday, January 20th 2007 was the start of the trip to the Microsoft headquarters in Redmond, WA for the first LEAP group (100 people). The second LEAP group (also 100 people) arrived a day later.
As I wrote in previous articles, the LEAP program consists of five masterclasses in The Netherlands and a set of presentations from Microsoft architects in the USA. Sunday, January 20th 2007 was the start of the trip to the Microsoft headquarters in Redmond, WA for the first LEAP group (100 people). The second LEAP group (also 100 people) arrived a day later.
Day 1
After a two hour drive, I arrived at the Amsterdam airport at 09:30, three hours before take-off. After a flight of more than eleven hours we arrived at Seattle airport, 16:00 hours local time.
A bus trip of half an hour took us to the Hyatt Regency hotel in Bellevue.
That evening, we formed groups to have dinner in the various restaurants in the neighborhood of the hotel. After that, we went to bed early, as it has been a very long day for all of us.
Day 2
Monday, we had a day for ourselves. It was a beautiful day, sunny and 5 degrees centigrade. With three colleagues I went to see Seattle.

We decided to take the bus from Bellevue to downtown Seattle. We visited the Pike Place market, the first Starbucks coffee shop, enjoyed the scenery around the harbor, visited the Space Needle, where had a great view over the Seattle city area from the 500 ft top floor.

After that, we went to see the famous Seattle aquarium and walked to the older part of the city. All in all a very interesting and entertaining day.
Day 3
On Tuesday, the real work started. We grouped at the hotel lobby at 07:00 to catch one of the three shuttle buses to the Microsoft campus.
After registration and a Microsoft supplied excellent breakfast, we attended the first presentation called "The architectural last mile", presented by Norm Judah. Norm told us architecture was about science (creating artifacts because of financial drivers), art (keeping it simple) and balancing between these two. The presentation contained many subjects, which made it a bit hard to see the point he was making.
After a short break, the second session, called "Software + Services: The Next Operational Challenge" started. This session was presented by Ulrich Homann. The problem with this presentation was that the title was a bit misleading. The actual title should have been "Capacity planning, now and in the future". It took me half the presentation to figure out what the goal of the talk was. I found out later that I was not alone in that. When looked from the Capacity planning angle, the presentation made much more sense.
After a good lunch and a walk around the Microsoft campus, two more presentations were given: "Internet Service Bus Overview" by Clemens Vasters and "Democratizing the Cloud with Volta" by Erik Meijer. These presentations were much better than the ones before lunch.

Clemens held a very inspiring talk about a kind of BizTalk service in the cloud, run by Microsoft, to be used by corporations. It contained live demo's, which actually worked. The same goes for Erik. He is a very interesting, enthusiastic, a bit chaotic speaker who talked about how to easily extend .Net programmers' knowledge to create multiple tier web applications. This presentations was mainly filled with live demo's, was very entertaining.
In the evening we were invited to the Parlor Billiards for an evening of Mexican food, beer and pool playing.
Day 4
This day started again with traveling to the campus and having a good breakfast.
The first presentation was "The New World of Work" by Dan Rasmus. He spoke about how he sees the new world, where much is changing: The workforce, the companies itself, etc. He spoke about the lumpiness of the world, instead of "The world is flat". If you look at top-10's of various subjects (education, work age, etc), most of the world is not in those lists, and is completely unseen in a flat world. Dan showed many statistics and much information. It will take me some time to digest all of this.

The second presentation by Kim Cameron was about (what else?) "Digital Identity". Kim is the author if the 7 laws of identity and the identity guru. He spoke about these laws and what they mean. He also introduced a new architecture for dealing with identities. A new concept for me was the concept of "claims" and transformations of claims. An example: In a hotel I claim to be Sjaak Laan by showing my passport and Visa card. In return (the transformation), the hotel gives me a hotel key (which is also a claim, because I could loose the key). These transformations of claims are also possible in more technical scemario's.
"Office Business Applications Overview" was presented by Karthik Ravindran. It was about the coupling of Office applications like Word, excel, Outlook and SharePoint with Line of Business (LoB) applications like SAP, Siebel, etc. After a short introduction we were presented with 3 demo's. The first two were very nice, combining Outlook appointments to a timesheet in the LoB application, using the new Ribbon feature of Office 2007. The second one was a Request for Proposal (RFP) document that was filled in using information from the underlying LoB application. Because of the limited time, the last demo was not very successful and hard to follow.
The last presentation was "The Irresistible Forces Meet the Movable Objects" by Pat Helland. This was by far the most interesting and entertaining presentation of all. He talked about Forces like changes in chips, power consumption, speed, storage, inreliable datacenters, flakey components, connectivity, etc. The Objects were the applications and data. Since the forces drive us forward, the objects have to move. This means that we have to make sure that future applications ad data are resilient for flakey hardware, unreliable connectivity, unsuccessful database inserts, failing datacenters or power, etc. The way to do this is a bit hard to explain, but it has to do with adapting applications to the way humans work. An example is that if you buy a book at Amazon, and the book falls on the floor in the warehouse, Amazon cannot ship you the book. They then apologize, which is fine, if it does not happen too often. Now if the book was not shipped because of a datacenter error, the effect would be the same for the customer. Therefore, in some cases it might be more cost effective to apologize (and maybe offer a small gift) than to built rock-solid IT systems. There is much more to say about this subject. Maybe I will write about this later.
In the evening we were taken to the New Castle Golf Course for an evening of excellent food and a spectacular view over Seattle by night.
Day 5
On this last LEAP day several workshops were given. I choose "Internet Scale Computing - the real stuff". This workshop actually was a set of three presentations.
The first one was about how the infrastructure behind www.microsoft.com is setup. I cannot say too much about this, as it is confidential, but the figures presented were very impressive.
The second presentation was about how the websites with high volumes of data and download (like hotmail.com, MSN.com and the security patch websites) were setup. The talk gave an insight on how many datacenters were necessary, and what could be done on the application side of things to keep this vast- and increasing amount of data flowing.
The third presentation was completely off-topic, because it was about robotics. It was very interesting though to see what Microsoft does in robotics software.
In the afternoon 60 lucky people, including me, were taken on a tour around the campus. Because I had to sign a non-disclosure agreement, I cannot say too much about this.
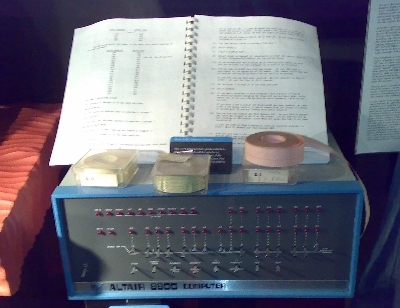
We did a visit to the home of the future which contained all cool gadgets, a visit to the Microsoft Visitors Center (which is sort of a Microsoft museum), a Center for Information Work tour (the office environment of the future) and made a visit to the company store, where people could buy Microsoft software and hardware for reduced prices.

In the evening we were invited to a Italian restaurant for dinner. I skipped that one, because I was very tired.
Day 6
This was the end of LEAP. We went to the Seattle/Tacoma airport for a flight back to The Netherlands, where we arrived at day 7, on 7:45 AM. All in all it was a very interesting trip. For me, the LEAP program was a big success.
I want to thank Dik Bijl, his team and Microsoft in Redmond for a terrific organization and a great learning experience.
This entry was posted on Sunday 27 January 2008
 Dutch
Dutch