Spam is big business
 Every day about 100 billion spam emails are sent. Of course, like most people you delete spam messages immediately, or you let your Internet provider delete them for you.
Every day about 100 billion spam emails are sent. Of course, like most people you delete spam messages immediately, or you let your Internet provider delete them for you.
But if only 0.001% of the sent spam lead to spending money (let's assume 10 dollar), every day 10 million dollar is earned in this business. This is about 3 billion dollar every year! And this seems like a conservative estimate.
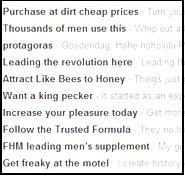
80% of all spam is being sent by some 200 spammers. Most of this spam is about selling medicine (drugs). In the USA and in most other countries most medication is only available with a doctor's prescription. In Canada, the rules are a bit less strict. Therefore spammers try their victims to persuade to order medicine from Canada (some medicines are apparently more popular than others for some reason...). The part they don't tell you is that you can order and pay for these medicines, but they get never delivered. This way spammers make money without making costs on products to ship. Of course one needs a good IT infrastructure to send the spam, but these IT infrastructures are just outsourced by the spammers.
Spammers use large botnets for sending al these billions of spam email, because of two reasons:
- Much bandwidth and CPU power is needed to send all the spam.
- Spammers don't like to be put out of business easily.
So, spammers need botnets. Because of this, criminal organizations exist that setup botnets using viruses. These organizations sell botnet services to spammers. Also they sell (stolen) email address lists to which the spam can be sent.
Every day about 1.2 million bots are created (i.e. new infected PC's that are setup to join a botnet). Bots that are used for some time are often not useable anymore, usually because the virus scanner of the particular PC switched off the bot software. On average, three days after the virus infection only half of the 1.2 million PC's are still useable. This means that new virus exploits are needed frequently to infect new PC's. The spammer does not need to create such exploits: it is the core business for yet other criminal organizations! These organizations hire crackers to find exploits. A new exploit costs about 100,000 dollar for the spammer. No problem, given the enormous year turnover the spammers make.
I think this a school example of organized crime, don't you?
This entry was posted on Saturday 25 October 2008
 Dutch
Dutch